Google Chrome Vulnerability Actively Exploited in the Wild
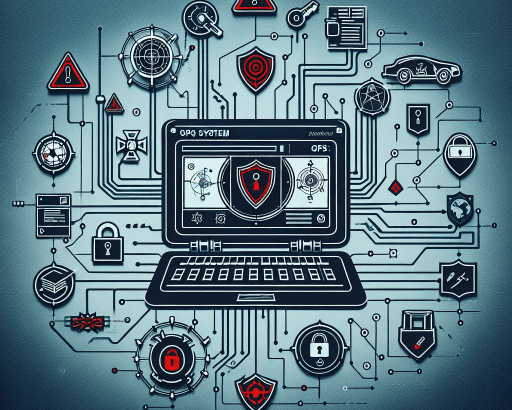
Google recently announced that a security flaw, tracked as CVE-2024-7965, which was patched in a recent security update for its Chrome browser, is being actively exploited in the wild. The vulnerability has been identified as an inappropriate implementation bug in the V8 JavaScript and WebAssembly engine, which powers the Chrome browser.
This critical flaw could allow malicious actors to execute arbitrary code on a victim’s device and potentially take full control. This type of vulnerability is a highly sought-after asset for cybercriminals, as it provides them with a significant advantage in launching successful attacks.
Immediate Action Needed to Prevent Exploitation
Users are urged to update their Chrome browsers to the latest version to mitigate the risk of falling victim to this exploit. Keeping software up to date is a crucial step in maintaining a secure computing environment and safeguarding sensitive information.
In addition to updating software, users should exercise caution while browsing the internet and avoid clicking on suspicious links or downloading attachments from unknown sources. Awareness and proactive security measures play a crucial role in preventing cyber threats.
Continuous Monitoring and Patching
It is essential for organizations to employ continuous monitoring of their systems and applications to detect any unusual activities that could indicate a security breach. Prompt patching of vulnerabilities is vital to prevent potential exploitation by threat actors.
Regular security assessments and penetration testing can help identify weaknesses in a system’s defense mechanisms and address them before they are leveraged by malicious entities. Taking a proactive approach to cybersecurity can significantly reduce the likelihood of successful attacks.
Collaborative Efforts in Cybersecurity
Cybersecurity is a collective effort that requires collaboration between individuals, organizations, and cybersecurity professionals. Sharing information about vulnerabilities and exploits helps raise awareness and enables swift action to address potential risks.
By staying informed about the latest security threats and best practices, individuals can play an active role in protecting themselves and their digital assets. Cybersecurity education and training are valuable tools in building a strong defense against cyber threats.
Conclusion
The active exploitation of the CVE-2024-7965 vulnerability in Google Chrome highlights the ever-present risks in the digital landscape. Timely updates, vigilant browsing habits, and ongoing security measures are essential components of a robust cybersecurity strategy.
By taking proactive steps to secure devices and networks, individuals and organizations can mitigate the impact of security incidents and reduce the likelihood of falling victim to cyber attacks. Stay informed, stay updated, and stay secure in the ever-evolving realm of cybersecurity.