Cybersecurity Researchers Unveil Vulnerability in Google Cloud Platform
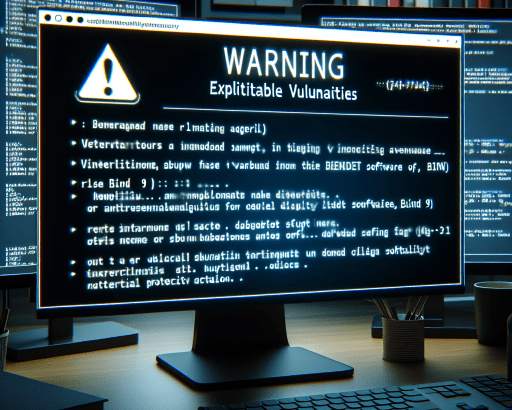
In the realm of cybersecurity, researchers have brought to light a critical privilege escalation vulnerability lurking within Google Cloud Platform’s Cloud Functions service. This flaw could potentially pave the way for malicious actors to breach other essential services and lay their hands on sensitive data, all without a shred of authorization.
Named by security experts as ConfusedFunction, this vulnerability poses a significant threat due to its potential for enabling attackers to boost their privileges and gain access to the pivotal Default Cloud Build Service Account. This could put at risk a plethora of confidential information and services that may be used by an attacker for nefarious purposes.
Understanding the Implications of ConfusedFunction
At its core, ConfusedFunction represents a critical weakness within the security architecture of Google Cloud Platform, allowing an attacker to maneuver their way into unauthorized areas that are otherwise inaccessible to them. By leveraging this vulnerability, threat actors can not only breach data and services within Cloud Functions but also potentially compromise other interconnected systems within the Google Cloud environment.
This escalation of privileges can trigger a cascade of security incidents, leading to severe repercussions for organizations relying on Google Cloud Platform for their operations. The unauthorized access that ConfusedFunction grants to attackers could lead to data breaches, manipulation of crucial resources, and even service disruptions that can wreak havoc on an organization’s digital infrastructure.
Implications for Google Cloud Users
For businesses and individuals utilizing Google Cloud Platform, the discovery of ConfusedFunction underscores the critical importance of staying vigilant and proactive when it comes to cybersecurity. Implementing robust security measures, conducting regular vulnerability assessments, and staying informed about emerging threats are imperative steps to safeguard digital assets and prevent falling victim to potentially devastating cyberattacks.
Upon learning about ConfusedFunction, Google Cloud users are urged to promptly address this vulnerability by implementing the necessary patches and security updates provided by the platform. By swiftly taking action to mitigate this risk, organizations can fortify their defenses and protect themselves against potential exploits that may stem from this security flaw.
Conclusion: Stay Secure, Stay Informed
In the ever-evolving landscape of cybersecurity threats, being aware of vulnerabilities like ConfusedFunction is essential for organizations and individuals to bolster their defenses effectively. By staying informed, proactive, and collaborative in addressing security risks, the cybersecurity community can strive towards creating a safer digital ecosystem for all. Remember, when it comes to cybersecurity, knowledge is power, and vigilance is key to thwarting potential threats before they materialize into full-blown security incidents.