Chinese Nation-State Threat Actor Targeting Japanese Organizations
A Chinese nation-state threat actor has set its sights on Japanese organizations, using sophisticated malware families such as LODEINFO and NOOPDOOR to steal sensitive information. Despite the cunning tactics employed by the threat actor, they have managed to fly under the radar for extended periods, sometimes up to two to three years.
Cybereason’s Discovery of the Cuckoo Spear Campaign
The Israeli cybersecurity firm Cybereason uncovered this ongoing cyber espionage campaign, which they have aptly named Cuckoo Spear. This campaign highlights the growing threat posed by nation-state actors and their relentless pursuit of valuable data.
Stealthy Operations and Extended Dwell Time
One of the standout characteristics of this Chinese threat actor is their ability to operate covertly and stealthily within compromised networks. By deploying malware like LODEINFO and NOOPDOOR, they can harvest sensitive information without raising any red flags. This stealthiness allows them to remain undetected for extended periods, enabling them to extract valuable data over a prolonged timeframe.
Implications for Japanese Organizations
For Japanese organizations, this targeted cyber espionage campaign represents a significant threat to their confidential information and business operations. The advanced tactics and prolonged dwell time of the threat actor make it challenging for organizations to detect and mitigate such attacks effectively.
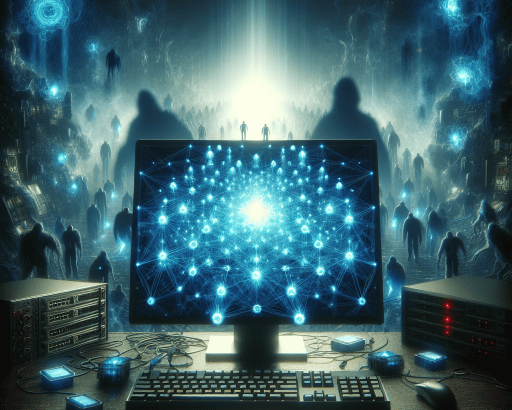
The Rise of Cyber Threats in the Digital Age
In today’s interconnected world, cyber threats are becoming increasingly sophisticated and pervasive. Nation-state actors, criminal organizations, and hacktivists are constantly evolving their tactics to infiltrate networks, steal data, and disrupt critical infrastructure.
The Importance of Vigilance and Proactive Security Measures
To combat these ever-evolving cyber threats, organizations must prioritize cybersecurity and implement robust defensive measures. Proactive monitoring, threat intelligence sharing, and employee training are essential components of a comprehensive cybersecurity strategy.
Collaboration and Information Sharing in the Cybersecurity Community
Cybersecurity firms like Cybereason play a crucial role in uncovering and neutralizing cyber threats through advanced threat hunting and analysis. By sharing their findings with the wider cybersecurity community, they help raise awareness and enhance collective defenses against malicious actors.
Protecting Sensitive Information and Safeguarding Networks
As the threat landscape continues to evolve, organizations must remain vigilant and proactive in defending against cyber threats. Implementing multi-layered security controls, conducting regular security assessments, and staying informed about the latest threats are key steps in safeguarding sensitive information and protecting networks from malicious intrusions.
In conclusion, the discovery of the Cuckoo Spear campaign targeting Japanese organizations serves as a stark reminder of the relentless cyber threats facing businesses today. By remaining vigilant, proactive, and collaborating within the cybersecurity community, organizations can enhance their defenses and mitigate the risks posed by sophisticated threat actors.