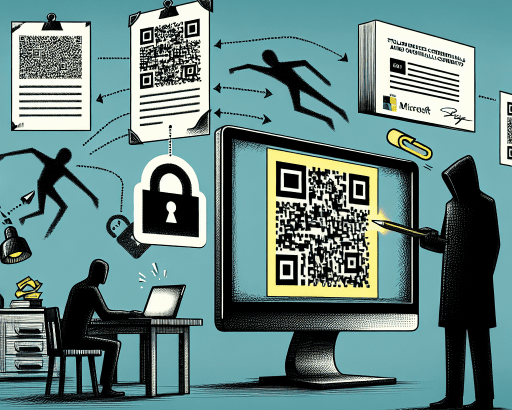
Exploit Campaigns Target Mobile Users
Cybersecurity researchers have recently uncovered several exploit campaigns aimed at compromising the security of mobile users. These campaigns specifically targeted vulnerabilities found in popular web browsers like Apple Safari and Google Chrome. By taking advantage of now-patched flaws in these browsers, cyber attackers were able to infect mobile devices with information-stealing malware. Despite patches being available for these vulnerabilities, the exploits were successful in infiltrating unpatched devices.
Google’s Threat Analysis Group (TAG) Findings
The Google Threat Analysis Group (TAG) played a crucial role in flagging these in-the-wild exploit campaigns. According to TAG researcher Clement, the attackers behind these campaigns deployed n-day exploits. These exploits were designed to target vulnerabilities that were already known to the software vendors, who had released patches to address them. However, the cybercriminals were able to effectively exploit these vulnerabilities on devices that had not been updated with the latest security patches.
Significance of Exploiting Unpatched Devices
The fact that these exploit campaigns were successful against unpatched devices underscores the importance of timely updates and security patches. Even when patches are available to fix known vulnerabilities, users who delay or ignore these updates are left vulnerable to cyber attacks. Cybercriminals often target unpatched devices knowing that they can exploit these known vulnerabilities to gain unauthorized access and deploy malware for malicious purposes.
Implications for Mobile Security
The exploitation of vulnerabilities in popular mobile browsers like Safari and Chrome highlights the ongoing challenges faced by mobile users in maintaining their cybersecurity. Mobile devices have become integral parts of our daily lives, storing sensitive information and connecting us to the digital world. However, this increased connectivity also exposes mobile users to various cyber threats, including malware infections and data breaches.
Best Practices for Mobile Security
To enhance mobile security and protect against potential exploit campaigns, it is essential for users to follow best practices such as:
1. Regularly update mobile operating systems and applications to apply the latest security patches.
2. Exercise caution when clicking on links or downloading attachments from unknown or suspicious sources.
3. Install reputable mobile security applications to detect and block malicious activities on your device.
4. Be cautious while accessing sensitive information on public Wi-Fi networks to prevent interception by cyber attackers.
5. Backup important data regularly to minimize the impact of a potential malware infection or data breach.
By adopting these proactive security measures, mobile users can significantly reduce their risk of falling victim to exploit campaigns and other cyber threats targeting mobile devices. Cybersecurity awareness and vigilance play a crucial role in safeguarding personal information and ensuring a secure mobile experience.